‘Tis the season to relax, indulge, and fall for a cyber scam. As you descend into a well-deserved break, one thing you shouldn’t ease up on is keeping an eye out for phishing attacks.

Phishing is the term for an online scam typically in the form of an email. Scammers try to convince you to share personal information or trick you into downloading something you definitely shouldn’t. $3.8 million has been lost to phishing this year in Australia, with Scamwatch recording almost 67,000 reports. That’s a 78% increase in loss and a 41% increase in activity from 2020.
“People must routinely refresh their anti-phishing cybersecurity knowledge because hackers never stop looking to exploit human weakness,” explains Dr Tina Wu, a cybersecurity expert at CSIRO’s Data61.
“Automated artificial intelligence (AI) phishing detection systems can struggle to deal with emerging attacks, the primary reason being their inability to perceive context in the same way as a human. Therefore, we need a collaborative human and artificial intelligence approach that utilises the capabilities of each.”
Dr Tina Wu and Dr Marthie Grobler are both cybersecurity experts at CSIRO’s Data61, specialising in the human element of cyber scamming and victim prevention. Both are leading a study to determine the factors behind why people still open suspicious emails, with the results to personally customise anti-phishing software.
“This real-time assessment infers individuals' unique cognition and emotion by recording and analysing eye-tracking data. This uniquely human element will then be integrated into anti-phishing software customised to the needs of each unique user.”
“While this will be a crucial tool in the kit against phishing attacks, you still need to know the latest tricks scammers are employing to catch you out.”
If you’re due for a refresher, these are Dr Wu and Dr Grobler’s recommendations on how you can identify and avoid some of the most commonly reporting phishing tactics this season:
Personal
It’s a bargain bonanza around Christmas and New Year, and while this is great for your wallet, falling for a phishing scam masquerading as an established brand won’t be.
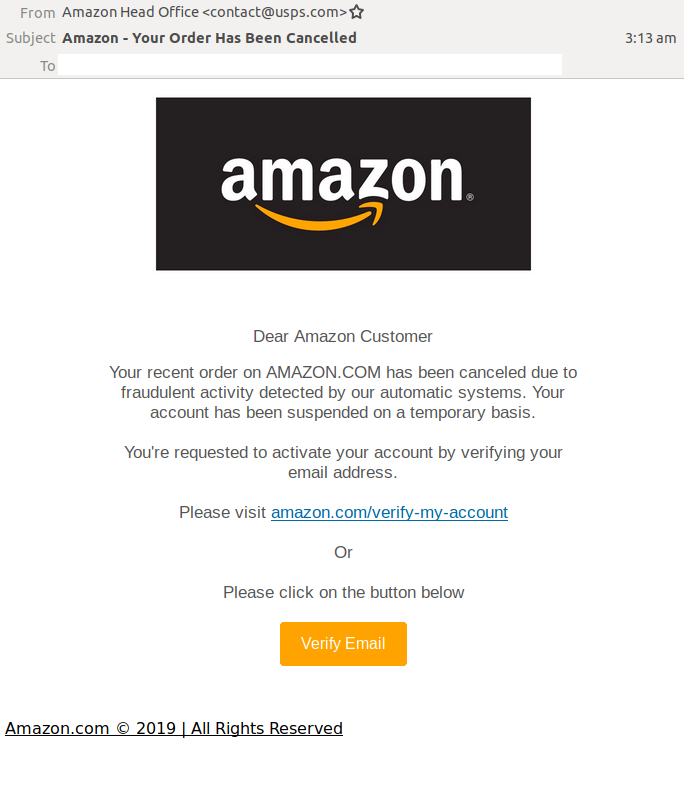
This type of scam leverages popular email marketing tactics, often mimicking or replicating the design of a brand’s eDM (electronic direct mail), using emotive language to elicit an immediate response, telling readers to click an external link, or login to their account.
Look out for:
- Unofficial email address. Carefully check the address for slight spelling changes, eg, eBaysupport.com rather than eBay.com, and e8ay rather than eBay. See if it matches previous legitimate correspondence and the address displayed on the brand’s authenticated website.
- Https over Http. Https signals that the website is encrypted, significantly decreasing the likelihood of hackers stealing your personal information. Hover over an external link with your cursor and the full address will be displayed on the bottom left of your screen.
- Shortened links. While not necessarily a sign of malicious activity, the technique is increasingly being used to conceal links to unencrypted and illegitimate sites. Run it through a URL expander to get a better look.
- Too good to be true prices. Sorry!
Example:
Work
Inherent trust in a workplace’s cyber security systems is a common factor in employees falling for phishing attacks, says Dr Grobler. "Not everything is picked up by spam folders. Avoidance techniques are becoming more sophisticated, like text padding with invisible characters and zero-point font obfuscation.”
“This is why employees need quarterly cyber security training and to vigilantly check each email.”
Double check:
- If the sender really is HR or payroll. There’s a rise in phishing scams impersonating organisational departments, particularly ones that might elicit anxiety and a fast response. These often take you to webpage that mimics the design of the legitimate version and ask you to enter in your login credentials.
- If that shared document link is genuine. “Links to shared documents, a common occurrence in the workplace, are now one of the most popular delivery methods for hacking organisations’ systems,” says Dr Wu. “It’s even overtaken malicious attachments and links.” Before inspecting the safety of the URL, ask yourself if you’re expecting this document and if you know who it’s coming from.
- The language. Is the tone, grammar and spelling off or unfamiliar?
Example:
Small to medium business owner
Renowned for high-level access and being busy, business owners are the perfect target for scammers.
Trending techniques include:
- Spear phishing. “There’s been a notable increase in phishing targeting senior positions within organisations,” says Dr Grobler. “These attacks are often well-researched and sophisticated, taking advantage of unique situations to penetrate an organisations’ cyber defences.” Watch out for requests to open a cloud service like Dropbox, Google Drive, Salesforce and Cisco Webex.
- Smishing, aka text message phishing. Scammers impersonating a bank, government agency or utility service will ask targets to confirm a payment, service or appointment via the provided link. The only thing you’ll be confirming once you click is a malware download.
- Fake invoice. An integral part of any business and an ingenious way to include a malicious attachment. If you’re not expecting it, don’t open it.
Example:
